Supervised and Sponsored by Chongqing Southwest Information Co., Ltd.
CODEN JKIEBK

 Guidelines
Guidelines-
1. Please use the Word edit layout and typeset the text in two-column layout.
2. We accept original research papers consisting of sections of introduction, related work,detailed method, technical descriptions, experimental verification and conclusion. In addition, we also accept review papers consisting of sections of introduction, questions and challenges, analysis on research status, research direction in the future and conclusion.
3. Peer-review fee for the submittedmanuscripts of original research is 150 RMB (normal) /300 RMB ( fast), while review papers can be processed with peer-review for free. The publishing fee is 150RMB / thousand words.
4. Format requirements for the text are as follows:
1) The font and size for Heading level 1 are “TimesNew Roman” and 7.5 points respectively.
2) The font and size for Heading level 2 are “Bold” and 10.5 points respectively.
3) The font and size for Heading level 3 are “Bold” and 9 points respectively.
4) The symbols, function names, variables and other changingparametersin the manuscriptshould be presented in italic.The parameters used shouldmeet the standard of legal unit of measurement.
5) The definitions, theorems, formulas, inference, algorithms, steps,the figures and tables should be numbered in order.
6) The graph should be processed by Microsoft? Visio, illustration text shouldbe clear in the picture.A sequence diagramshould include a diagram name and the order for the diagram.The line weight is 0.5pt, the line color is bold. The width of the drawing is generally less than 8cm in a single-column layout and the width should be no more than 13-14cm in a two-column layout. The sample of Fig. is as follows.

Fig.1 Simplified CG of the benign andthe malicious
7) The figure number and figure caption should be placed in the middle below the drawings.
8) The number and title of tables should be placedin the middle below under the tables.
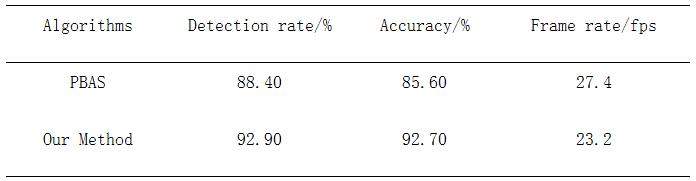
9) Make your columns in three-line tables, for example:
Table 1 Example table
5. The format and standardization of reference description are as follows:
[1]OH S, PARK S. Task–role-based access control model[J]. Information systems, 2003, 28(6): 533-562.
[2]KALAL Z,MATAS J. P-N Learning: Bootstrapping Binary Classifiers by Structural Constraints[C]// Proceedings of IEEE Conference on Computer Vision and Pattern Recognition. New York: IEEE Press, 2010:49-56.
[3] BUGIELS, DAVIL,DMITRIENKO A, et al. Xmandroid: A new android evolution to mitigate privilege escalation attacks:TR-2011-04 [R]. Dresden :TechnischeUniversitadt Darmstadt, 2011.
[4]RIVEST R L, ADLEM A L, DERTOUZOS M L.On Data Banks and PrivacyHomomorphism [M]// New York: Academic Press, 1978: 169–179.
[5]WANG Y. Research on Software fault localization method based on fault propagation context analysis[D].Harbin: Harbin Institute of Technology,2013.
[6] W3C.Web Service Choreography Interface(WSCI)(Version1.0)[EB/OL].www.w3.org/TR/wsci.
6. Please adopt the only website http://www.jsjkx.com to submit paper online. We only accept submissions via this system, and do not accept printed contributions and email forms of contribution. Before uploading your manuscript, you must make sure the file is not infected with viruses.
7. In order to contact timely, when submitting the manuscript, please provide a communication author (including mailing address, zip code, E-mail address and telephone number, etc.). During the peer-review process, if there is any change of contact, please inform the editorial office. Please specify whether you are CCF members (accompanied by member number), as the article of the first author being the CCF members can get all costs 85% discount.


 Home
Home
